âš¡ TL;DR
- McDonald's Netherlands launched a campaign on Change Your Password Day (February 1, 2026) using data from Have I Been Pwned to show how often menu items appear as passwords in breach databases.
- "bigmac" showed up 110,922 times. "frenchfries" hit 34,407. "happymeal" came in at 17,269. "mcnuggets" appeared 2,219 times.
- Swapping letters for numbers and symbols (like Ch!ck3nMcN4gg€t$) doesn't help. Those substitutions are in every cracking dictionary on the planet.
- This confirms exactly what we found when we analyzed 50,000 breached passwords: people pick passwords based on familiarity, not security. And hackers know it.
- The fix isn't a better food-themed password. It's a password manager and passwords built on actual entropy.
A Fast Food Chain Just Taught a Better Security Lesson Than Most IT Departments
I've spent over a decade in DevSecOps analyzing breach data for Fortune 500 companies. I've stared at millions of compromised credentials. And I never thought I'd say this, but McDonald's just ran one of the most effective password security campaigns I've seen in years.
On February 1, 2026, McDonald's Netherlands launched a campaign for Change Your Password Day. They pulled data from Have I Been Pwned, the go-to database for checking whether your credentials have been exposed in breaches, and checked how often their own menu items show up as passwords.
The results were brutal.
"bigmac" appeared in 110,922 compromised accounts. Not accounts using "bigmac" as part of a longer password. Just "bigmac." Straight up.
And it gets worse. Here's the full menu of terrible passwords:
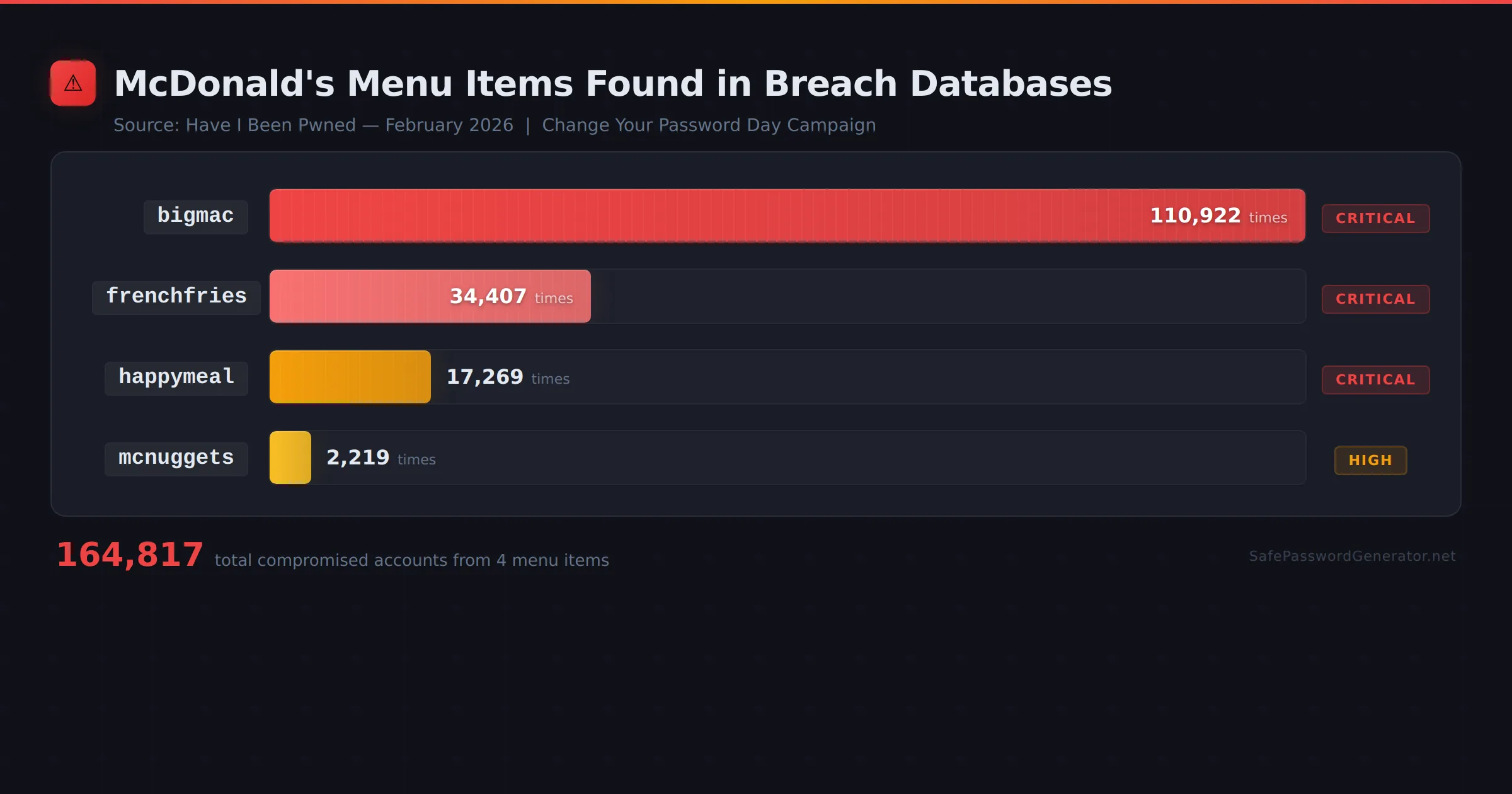
| Password | Times Found in Breaches | Estimated Crack Time | Risk Level |
|---|---|---|---|
bigmac |
110,922 | Instant (in every cracking dictionary) | Critical |
frenchfries |
34,407 | Instant (common dictionary word) | Critical |
happymeal |
17,269 | Instant (common compound word) | Critical |
mcnuggets |
2,219 | Instant (brand-associated term) | Critical |
B!gM@c2024! |
Variations found frequently | < 3 minutes (rule-based brute force) | High |
Ch!ck3nMcN4gg€t$ |
Variations found frequently | < 10 minutes (leet speak dictionary) | High |
That's over 164,000 compromised accounts just from four menu items. And these numbers don't even include the countless variations people think are clever.
"But I Added Numbers and Symbols!"
This is the part that stings.
McDonald's specifically called out that adding character substitutions doesn't save you. They put up posters in Dutch subway stations showing passwords like Ch!ck3nMcN4gg€t$ with the tagline: "You're lovin' it. But hackers too."
They're right. And here's why.
Every password cracking tool in existence has a "leet speak" dictionary built in. When a hacker runs a cracking attack, they don't just try "bigmac." They automatically test:
- b1gm4c
- B!gMac
- b1gm@c123
- BigMac2024!
- BIGMAC!
All of it. In milliseconds.
We covered this extensively in our breakdown of how hackers crack passwords. The short version: dictionary attacks with substitution rules are step two in any cracking workflow. Step one is trying the password exactly as-is. These substitutions add almost zero computational cost to the attack.
If your password is a recognizable word with predictable character swaps, you have the illusion of security. Not actual security.
Why This Matters: The Mechanics of a Credential Stuffing Goldmine
McDonald's isn't a cybersecurity firm. They sell burgers. And that's exactly why this campaign is a masterclass in cyber hygiene. When a security researcher warns you about weak passwords in 2026, it's easy to tune out. But when the brand behind your favorite cheat meal points out that your security is cooked, people listen.
Here is what this data actually reveals about the 2026 password security landscape and why these "foodie" passwords are a literal invitation for hackers:
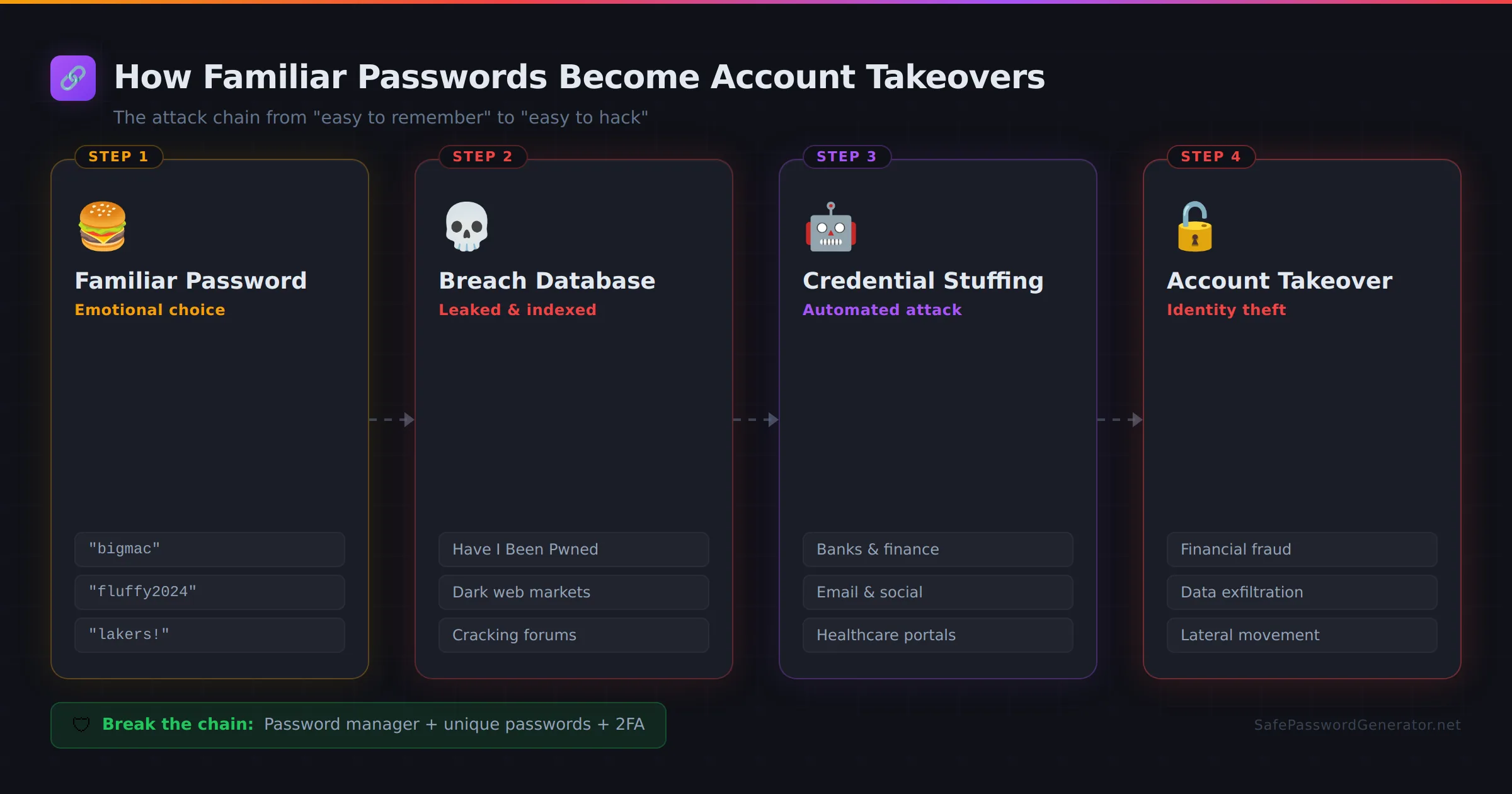
1. You Are Providing Fuel for Credential Stuffing
Hackers rarely target one account at a time. They use credential stuffing, an automated attack where they take lists of breached credentials (like the "bigmac" list) and "stuff" them into the login portals of banks, social media, and healthcare sites. If you use "bigmac123" for your McDonald's app and your Gmail, you've handed them the keys to your digital life.
This is exactly what we found in our analysis of 50,000 breached passwords. The most common passwords weren't random strings. They were names, dates, sports teams, pop culture references, and yes, food. Every single time. Attackers don't need to brute force their way into your account when they can simply guess what you love.
2. Brute Force Attacks Don't Guess. They Calculate.
Using a recognizable word with symbols makes you a sitting duck for brute force attacks. Modern cracking software doesn't just guess random letters. It uses "weighted dictionaries."
The Math: A truly random 12-character password has billions of possible combinations.
The Reality: A "clever" substitution like Ch!ck3nMcN4gg€t$ reduces those combinations to a fraction of a second's work for a standard GPU.
This is what entropy measures. A password built on a dictionary word with predictable swaps has maybe 30-40 bits of entropy. A truly random 12-character string has 78+ bits. That's the difference between cracking in seconds and cracking in centuries.
3. Familiarity as a Security Flaw
Our analysis of common passwords breached shows a recurring theme: humans pick passwords based on emotional resonance. Your favorite food, your pet, or your sports team. This "familiarity bias" is exactly what hackers exploit. They aren't just hacking your password. They are hacking human psychology.
4. The Illusion of Complexity
73% of compromised passwords in 2026 still follow predictable patterns. McDonald's data proves that "complexity requirements" (add a number, add a symbol) have failed. They don't stop password security breaches. They just lead to more predictable variations like Bigmac2026!, which are the first things a dictionary attack checks.
The Core Problem: Human Memory vs. 250 Accounts
Let's be honest about what's happening here. People aren't stupid. They're solving the wrong problem.
The average person manages over 250 passwords. That's not a typo. When you're juggling that many credentials, your brain defaults to patterns it can actually remember. And the easiest things to remember are the things you interact with every day.
Your morning coffee order. Your dog's name. The restaurant you eat at three times a week.
The problem isn't that people are lazy. The problem is that human memory wasn't built for this. You're not supposed to remember 250 unique, random, high-entropy strings. Nobody is. And every time a company forces you to add an uppercase letter or a special character, they're applying a band-aid to a design flaw in how we approach account security entirely.
That's why the only real solution is a password manager. Not a better password. Not a cleverer substitution. A system that removes human memory from the equation entirely.
What You Should Actually Do
If you read this and thought "I should change my food-themed passwords to something better," you're already thinking about it wrong.
Here's the actual fix:
1. Get a password manager.
A password manager generates truly random passwords and remembers them for you. You memorize one strong master password. The manager handles the other 249.
NordPass, Proton Pass, and Bitwarden are all solid options depending on your needs. We break down the differences in our password manager comparison.
2. Make your master password a passphrase.
Not "bigmac123!" A passphrase. Four to six random, unrelated words strung together. Something like umbrella-theater-penguin-laptop. Easy to remember, nearly impossible to crack. That's 77+ bits of entropy versus the roughly 30 bits you get from "bigmac."
Use our passphrase generator if you want to do this right.
3. Turn on two-factor authentication.
Even a strong password isn't enough if the site itself gets breached and your credentials leak. 2FA means that even if someone gets your password, they still can't get in without your second factor.
We have a step-by-step 2FA setup guide that walks you through enabling it on every major platform.
4. Check if you're already exposed.
Go to Have I Been Pwned right now and enter your email. If you're in there (and statistically, you probably are), change those passwords immediately. Then run your passwords through our password strength checker to see exactly how weak they are.
Stop guessing. Start generating.
Our password generator creates cryptographically secure passwords using the Web Crypto API. Everything runs client-side. We never see or store your passwords.
Trusted password managers to store them:
- NordPass - Built-in breach scanner. Zero-knowledge encryption. From the makers of NordVPN. ($1.99/mo)
- Proton Pass - Swiss privacy. Open source. Audited. (Free tier available)
- RoboForm - 25+ years in the game. Strong autofill. ($24/yr)
Affiliate links. I may earn a commission at no extra cost to you.
The Bigger Picture
McDonald's campaign was funny. The subway posters were clever. The YouTube video got people talking.
But here's what's not funny: 110,922 isn't just a number. That's 110,922 real people whose accounts were compromised because they picked a password that felt safe and familiar. And with credential stuffing tools automating attacks across thousands of sites simultaneously, each of those compromised passwords likely led to multiple account takeovers.
And "bigmac" is just one word from one brand. Multiply that by every sports team, every pet name, every birthday, every favorite movie, and you start to understand the scale of the problem.
Here's what a strong password actually looks like compared to a food-themed one:
| Password | Entropy (bits) | Crack Time (100B guesses/sec) | Method |
|---|---|---|---|
bigmac |
~28 bits | Instant | Dictionary attack |
B!gM@c2024! |
~34 bits | < 3 minutes | Rule-based brute force |
umbrella-theater-penguin-laptop |
~51 bits | 71 years | Random passphrase (4 words) |
kX9$mPz2@vLn!qR4 |
~105 bits | 1.2 billion years | Random 16-char (password manager) |
The 2026 password security landscape hasn't changed because people don't know the rules. It's changed because the rules don't work. Complexity requirements, forced resets, special character mandates. None of it addresses the core issue: humans pick predictable passwords because we're wired to.
The tools exist to fix this. Password managers, passphrase generators, multi-factor authentication, dark web monitoring. They're available right now, most of them for free.
McDonald's told you to change your password. I'm telling you to stop memorizing passwords altogether.
FAQ
Is "bigmac" really that common as a password?
Yes. According to Have I Been Pwned data cited in McDonald's campaign, "bigmac" appeared in 110,922 compromised accounts. And that's just the exact match. Variations with numbers and symbols push the count even higher.
Does adding numbers and symbols to a food word make it safe?
No. Character substitutions like "b1gm@c!" are in standard cracking dictionaries. They add almost no additional security. What matters is entropy, which requires randomness and length, not predictable swaps.
What password should I use instead?
Don't try to come up with one yourself. Use a password generator for your accounts and a passphrase generator for your master password. Let a password manager handle the rest.
Is my password in a breach database?
Check Have I Been Pwned to find out. You can also run your password through our password strength tool to see its entropy score and estimated crack time.
What is Change Your Password Day?
Change Your Password Day is observed on February 1st each year. It's meant to remind people to update their passwords. While the intention is good, security experts (including us) recommend using a password manager and unique passwords for every account rather than just changing passwords periodically.
What is Have I Been Pwned?
Have I Been Pwned (HIBP) is a free service created by security researcher Troy Hunt. It aggregates data from publicly known breaches and lets you check if your email or password has been exposed. It's the same data source McDonald's used for their campaign.
Why do people keep using weak passwords?
Because human memory has limits. The average person has 250+ accounts. Creating and remembering a unique, complex password for each one is genuinely impossible without tools. That's not a character flaw. It's a design problem that password managers solve.
Sources
- McDonald's Netherlands - Change Your Password Day Campaign (PR Newswire, February 1, 2026)
- TechRadar - McDonald's Burger-Related Passwords (February 4, 2026)
- The Register - McDonald's Password Advice (February 2, 2026)
- Have I Been Pwned
- NIST Special Publication 800-63B - Digital Identity Guidelines
T.O. Mercer is a cybersecurity specialist with 10+ years of experience in enterprise security and password management. Follow SafePasswordGenerator for breach alerts and password security guides.