Your company isn't being hacked. It's being audited by criminals.
In 2026, ransomware gangs operate less like hackers and more like private equity firms. They have target scoring models, ROI calculations, and even "customer" support. If you're hit, it's because a spreadsheet told them you were worth the effort.
I've spent over a decade in enterprise security at Fortune 500 companies. What still surprises me is how many people think ransomware is random bad luck.
It's not. These groups maintain internal databases ranking organizations by payment history, cyber insurance coverage, and network complexity. Every attack is a calculated investment decision.
Executive Summary
The 2026 ransomware landscape has shifted from encryption-first attacks to identity-centric exploitation. Gangs now prioritize targets with leaked credentials (54% of victims appeared in credential dumps before attack), unpatched vulnerabilities (60% of attacks exploit CVEs over 90 days old), and high-pressure industries like Healthcare ($5,000+ per network access). Initial Access Brokers (IABs) serve as the "deal sourcing" arm, with session token theft (MFA bypass) now commanding 30-50% premiums over standard credentials. The primary defense in 2026: identity-centric security including unique passwords, MFA everywhere, session monitoring, and assuming your credentials are already compromised.
Table of Contents
- The 2026 Ransomware Landscape: What Changed
- The 3-Step Attack Chain: How IABs and Infostealers Choose the Target
- The "Market Rate" for Your Company's Access
- Why Certain Industries Command Premium Prices
- AI-Driven Audits: How Gangs Automate Your Valuation
- Your Leaked Password Is the First Domino
- Double Extortion: Why Encryption Is No Longer the Main Threat
- Red Flags: Signs Your Company Is Being "Audited"
- What You Can Do Today (Not Tomorrow)
- The Business Reality: Why This Won't Stop
- FAQ: Ransomware Victim Selection
The 2026 Ransomware Landscape: What Changed
The data from 2025 set the baseline. What we're seeing in 2026 is an acceleration of the trends that were already emerging.
| Metric | 2025 Baseline | 2026 Trend |
|---|---|---|
| Total Global Attacks | 7,419 (up 32% from 2024) | Pace continuing upward |
| Encryption Rate | 50% of victims | 49% (5-year low) |
| Data Theft Extortion | Rising | Now exceeds encryption ROI |
| Median Dwell Time | 12-22 days | 4 days |
| Average Incident Cost | $5.08 Million | Holding steady |
| Median Ransom Payment | $115,000 | Slight decline |
| Compromised Credentials Entry | 23% of attacks | Growing as MFA bypass matures |
The critical shift: encryption rates have hit a 5-year low at 49%.
Attackers realized that stealing data and threatening leaks is quieter, harder to detect, and often more profitable than encrypting systems. Why trigger backup recovery when you can just threaten to publish executive emails?
Here's the stat that should keep you up at night: 54% of ransomware victims had their company domains appear in infostealer credential dumps before the attack.
Your leaked password isn't just a personal problem. It's a targeting signal.
The 3-Step Attack Chain: How IABs and Infostealers Choose the Target
Ransomware groups don't do their own reconnaissance anymore. They've outsourced it.
Step 1: Industrial-Scale Scanning
Tools like Shodan and Censys identify 3.2 billion exposed services daily across IPv4 space. They're filtering for:
- Unpatched vulnerabilities (60% of attacks exploit known CVEs over 90 days old)
- Exposed remote desktop services
- Weak VPN configurations
Step 2: Initial Access Brokers (IABs) Do the Dirty Work
This is where it gets interesting.
IABs are specialized criminals who do nothing but gather intelligence and sell network access. They don't deploy ransomware themselves. They just sell the keys.
Think of them as the "deal sourcing" arm of a private equity operation.
They buy compromised credentials from infostealer marketplaces, validate them, package them up, and resell to ransomware operators.
The underground marketplace operates like legitimate e-commerce: reputation systems, customer support, money-back guarantees.
The 2026 Premium: Session Token Theft
Here's what changed this year. Standard username/password combos are becoming commoditized.
The new gold? Stolen session cookies that bypass MFA entirely.
An IAB listing with a verified session token (MFA bypass) now commands a 30-50% premium over standard credentials. Why? Because the buyer doesn't need to worry about 2FA prompts, security questions, or device verification.
They just import the cookie and they're in.
Insider Note: In my time securing enterprise environments, I've seen IAB listings appear on dark web forums within 12 hours of a third-party vendor breach. But the speed has accelerated. Current intel shows the median time from initial access purchase to ransomware deployment is now just 4 days. By the time your security team gets the breach notification email, the attackers may already be exfiltrating data.
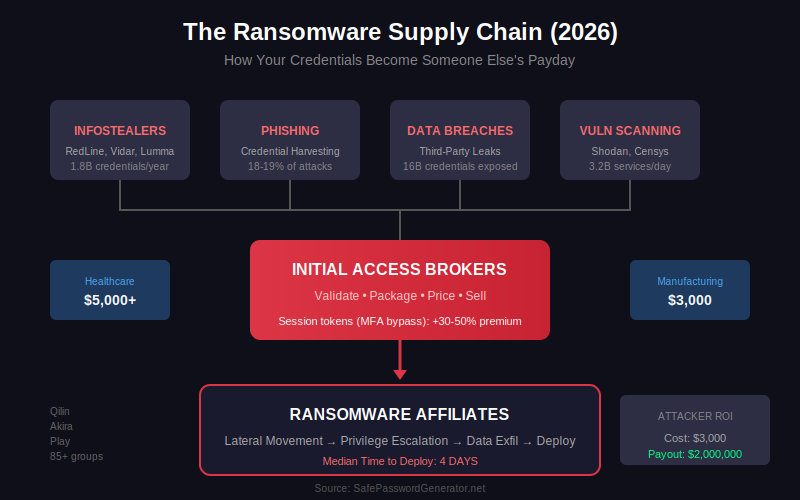
Step 3: The Ransomware Affiliate Closes the Deal
Once an affiliate buys access, they move laterally, escalate privileges, exfiltrate data, and deploy ransomware.
If it costs a broker $3,000 to get in and the payout is $2 million, that's an ROI a venture capitalist would kill for.
The "Market Rate" for Your Company's Access
Here's what your network access is worth on the dark web in 2026:
| Target Industry | Access Price (Avg) | Why This Price? | 2026 Trend |
|---|---|---|---|
| US Healthcare | $5,000+ | Patient data value + 72-hour life/death pressure | Stable |
| Manufacturing | $3,000 | $100k/hour downtime + supply chain leverage | ↑ 61% attack growth |
| Legal/Law Firms | $4,000-$6,000 | Triple extortion: data + litigation + client BEC | ↑ High priority |
| Education | $500-$1,000 | High volume of weak credentials, low security budgets | Stable |
| Government | $1,500-$3,000 | Data value for nation-state resale | Stable |
Manufacturing saw the steepest growth entering 2026, with attacks surging 61% year-over-year.
The reason? Supply chain pressure. When an automotive plant goes down, the ripple effects hit dozens of companies. That leverage translates directly into higher ransom payments.
A Fortune 500 executive's credentials? That can fetch $50,000.
Generic consumer accounts trade for $10-$50.
The price reflects one thing: how much leverage the attacker gains from that access.
Why Certain Industries Command Premium Prices
Ransomware gangs maintain what security researchers call "sector profitability matrices."
It's cold, calculated economics. They balance disruption costs against payment likelihood.
Healthcare (28% of Q1 2025 victims)
Hospitals face immediate patient risk. A 72-hour payment deadline during surgical season maximizes pressure.
Healthcare PII sells for $10 per record on dark web markets versus $0.50 for generic email addresses.
The Change Healthcare attack in 2024 disrupted 15% of US prescriptions. Recovery costs hit $40 million.
Manufacturing (15% of victims, 61% attack growth)
Extended downtime costs roughly $100,000 per hour for automotive plants.
The Cl0p campaign against Cleo MFT in early 2025 hit 348 manufacturers simultaneously, extracting over $20 million through coordinated supply chain pressure.
Insider Note: I worked with a manufacturing client whose production line went down for 6 hours due to a ransomware "test" deployment. The attackers never even asked for payment. They were validating the access before selling it to a bigger operator. That's how sophisticated the supply chain has become.
Legal Firms (Rising Priority for Triple Extortion)
Law firms are increasingly targeted because they offer three leverage points:
- Data extortion: Confidential client information
- Litigation leverage: Ongoing case materials
- BEC enablement: Client contact lists for follow-on attacks
A single law firm breach can cascade into attacks on dozens of their corporate clients.
AI-Driven Audits: How Gangs Automate Your Valuation
This is the 2026 development most security teams haven't caught up to yet.
Ransomware gangs are now using LLMs and AI tools to industrialize their "target audit" process. They aren't just looking for your password anymore. They're parsing your stolen data for intelligence that sets the ransom amount.
What AI Is Scanning For:
When an infostealer dumps your email archive or document cache, it doesn't go to a human analyst first. It goes through automated parsing that looks for:
- Insurance policy limits (cyber liability coverage amounts)
- Upcoming M&A activity (merger dates, acquisition targets)
- Executive compensation data (ability to pay)
- Vendor relationships (supply chain leverage points)
- Regulatory exposure (HIPAA, GDPR, SOX compliance gaps)
If your stolen emails mention "our cyber policy covers up to $5 million," congratulations. Your ransom demand just got calibrated.
The "Target-Rich Keywords" Problem
Gangs have keyword lists that flag high-value targets. Terms like "board meeting," "due diligence," "insurance renewal," and "confidential settlement" trigger elevated attention.
This is why email hygiene matters beyond just phishing. Every email you send is potential intelligence for ransom calibration if your network is breached.
The defenders who understand this are already implementing data classification and DLP (Data Loss Prevention) not just for compliance, but for ransom risk reduction.
Your Leaked Password Is the First Domino
Here's where this connects directly to you.
Compromised credentials are the initial access vector in 23% of ransomware attacks. Only vulnerability exploitation (32%) is higher.
But that 23% understates the real problem.
Many exploited vulnerabilities only become exploitable after attackers use stolen credentials to get inside the network first.
The numbers are staggering:
- Check Point reported a 160% increase in compromised credentials in 2025 vs 2024
- Infostealers harvested 1.8 billion credentials last year
- One 2025 mega-leak exposed approximately 16 billion credentials
- Verizon DBIR found 54% of ransomware victims had domains in infostealer dumps beforehand
The average company takes 94 days to discover their credentials have been compromised.
And 94% of passwords are reused across multiple sites.
When one gets popped, everything connected to it becomes vulnerable.
Double Extortion: Why Encryption Is No Longer the Main Threat
Here's the shift most people haven't caught up to: only 49% of ransomware victims in 2026 experienced data encryption.
That's the lowest encryption rate in five years.
Why? Because encryption is noisy. It triggers alerts. It activates backup recovery processes.
Data theft is quieter and often more profitable.
How Double Extortion Works:
- Attackers gain access (via stolen credentials or exploited vulnerability)
- They spend days or weeks quietly exfiltrating sensitive data
- They may or may not encrypt systems
- They threaten to publish stolen data on leak sites if you don't pay
Double extortion generates 340% higher payments than encryption-only attacks.
The leverage is different. With encryption, you're paying to get your systems back. With data theft, you're paying to prevent reputational destruction, regulatory fines, and lawsuits.
Healthcare records, legal documents, and financial data carry indefinite resale value even after you pay.
Some groups have moved to triple extortion: encryption + data theft + DDoS attacks on your public-facing services while you're trying to recover.
Red Flags: Signs Your Company Is Being "Audited"
Ransomware attacks don't happen instantly. There's usually a reconnaissance and staging period.
But that window is shrinking. In 2022, you had 16 days to catch an intruder. In 2026, the median dwell time is 4 days.
You aren't fighting a hacker. You're fighting a stopwatch.
"In 2022, you had 16 days to catch an intruder. In 2026, the median dwell time is 4 days. You aren't fighting a hacker; you're fighting a stopwatch."

Watch for these warning signs:
Network & Access Anomalies
- VPN logins from unusual geographic locations (especially countries where you have no employees)
- Successful logins at unusual hours (3 AM local time)
- Multiple failed login attempts followed by a successful one
- New user accounts appearing without IT tickets
Scanning & Probing Activity
- Surge in port scanning against your external IP ranges
- Unusual DNS queries to known malicious domains
- Unexpected outbound traffic to cloud storage services (Mega, Dropbox, etc.)
Endpoint Behavior
- Security tools being disabled or uninstalled
- PowerShell or command-line activity on machines that don't normally use it
- Large file archives being created (attackers staging data for exfiltration)
- Shadow copy deletion attempts
Credential Indicators
- Your company domain appearing on HaveIBeenPwned or dark web monitoring alerts
- Reports of phishing emails impersonating your executives
- Password reset requests you didn't initiate
- Session anomalies (same user logged in from multiple locations simultaneously)
If you see three or more of these simultaneously, assume you're in the "validation" phase and escalate immediately.
What You Can Do Today (Not Tomorrow)
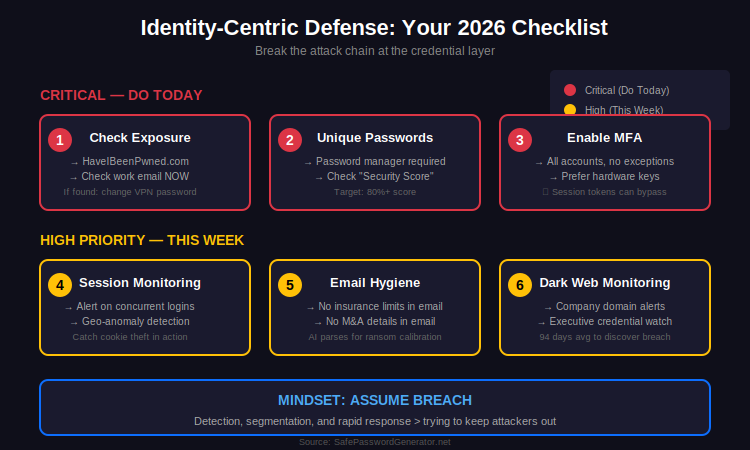
I'm not going to pretend there's a simple fix. Ransomware defense requires layers.
But identity-centric security is the piece most individuals and small organizations can control right now.
1. Check Your Exposure First
Go to HaveIBeenPwned.com right now. Check your work email.
If it's there, change your VPN and email passwords before you finish your coffee.
2. Unique Passwords for Everything
Not variations. Completely different passwords.
A password manager makes this practical. Check your "Security Score" in your browser or manager today. If it's below 80%, you have work to do.
3. Enable MFA Everywhere (But Understand Its Limits)
MFA is still essential. But session token theft means MFA isn't bulletproof.
Consider phishing-resistant MFA (hardware keys like YubiKey) for critical accounts. Monitor for session anomalies, not just login events.
4. Assume Breach
The defenders I respect most operate with the assumption that someone already has valid credentials to their environment.
They focus on detection, segmentation, and rapid response rather than solely trying to keep attackers out.
5. Email Hygiene for Ransom Reduction
Given AI-driven valuation, be cautious about what you put in email. Insurance limits, M&A details, and executive compensation discussions are all ransom calibration data if your network is breached.
The Business Reality: Why This Won't Stop
Ransomware operators treat law enforcement disruption as an 8-12% operating cost.
When LockBit got taken down, they rebranded within 48 hours.
There are now 85+ active ransomware groups operating simultaneously. 45 new groups appeared in 2025 alone, and the fragmentation continues into 2026.
The economics favor the attackers:
- Double extortion (encryption + data theft) generates 340% higher payments than encryption alone
- Average incident costs hit $5.08 million
- Even though 64% now refuse to pay, the 36% who do pay make it profitable
In 2022, you had 16 days to catch an intruder. In 2026, the median dwell time is 4 days. You aren't fighting a hacker; you're fighting a stopwatch.
The "good" news: refusing to pay is becoming more common, and backups enable faster recovery.
The bad news: gangs are adapting by stealing data and threatening leaks even without encrypting systems. And AI is making their target selection more precise.
FAQ: Ransomware Victim Selection
How do ransomware gangs find their victims?
Ransomware groups use industrial-scale internet scanning to identify vulnerable systems, then rely on Initial Access Brokers (IABs) who purchase and validate stolen credentials from infostealer marketplaces. They prioritize targets based on industry, revenue, insurance coverage, and payment history. In 2026, AI tools are increasingly used to parse stolen data for target valuation.
What is an Initial Access Broker (IAB)?
An Initial Access Broker is a specialized cybercriminal who focuses solely on gaining and selling network access. They don't deploy ransomware themselves. Instead, they buy credentials from infostealer operators, validate the access works, and resell it to ransomware affiliates. Prices range from $500 for education targets to $5,000+ for healthcare organizations. Session tokens that bypass MFA now command 30-50% premiums.
Why is healthcare the most targeted industry for ransomware?
Healthcare organizations face unique pressure: patient safety concerns create 72-hour payment urgency, regulatory fines (HIPAA violations can exceed $800,000), and healthcare records sell for 20x the price of generic credentials on dark web markets. This combination makes them high-value, high-pressure targets.
How do I know if my credentials have been compromised?
Check HaveIBeenPwned.com for your email addresses. Many password managers also include dark web monitoring. If your domain appears in known breaches, assume attackers have tested those credentials against your VPN, email, and cloud services.
What is double extortion ransomware?
Double extortion combines data encryption with data theft. Attackers steal sensitive files before encrypting systems, then threaten to publish the stolen data on leak sites if the ransom isn't paid. This tactic generates 340% higher payments than encryption-only attacks because victims face both operational disruption and reputational/regulatory damage. In 2026, encryption rates have fallen to 49% as data theft becomes the primary leverage.
What is the current ransomware dwell time?
Median dwell time (the period between initial access and ransomware deployment) has shrunk to approximately 4 days in 2026, down from 12-22 days in previous years. This compressed timeline means organizations have less time to detect and respond to intrusions before damage occurs.
The Bottom Line
Every credential leak represents a potential entry point.
When ransomware groups scan infostealer dumps looking for targets, your company's domain appearing in that list moves you up their priority ranking.
Strong, unique passwords managed properly won't stop a determined nation-state actor.
But they will remove you from the target-rich environment that ransomware gangs prefer. They go after the easy wins first: organizations with known credential exposures, unpatched systems, and weak authentication.
The first step to not being the easy win?
Check your work email on HaveIBeenPwned right now. If it's compromised, change your VPN password before you close this tab.
About the Author: This analysis comes from a Senior Solutions Engineer with 10+ years of DevSecOps experience at Fortune 500 companies, specializing in enterprise security and observability.
Sources: The420.in | Check Point Research | Comparitech | SOCRadar | IBM Security | Verizon DBIR | BlackFog | Sophos | World Economic Forum