By T.O. Mercer · April 27, 2026 · 8 min read
ADT Breach 2026: 5.5 Million Records Stolen With One Phone Call
Today is the ransom deadline ShinyHunters set for ADT. As of publication, the stolen data has not been publicly leaked. Have I Been Pwned has confirmed 5.5 million records in the breach. ADT has not responded publicly to the ransom demand. This article will be updated as the situation develops.
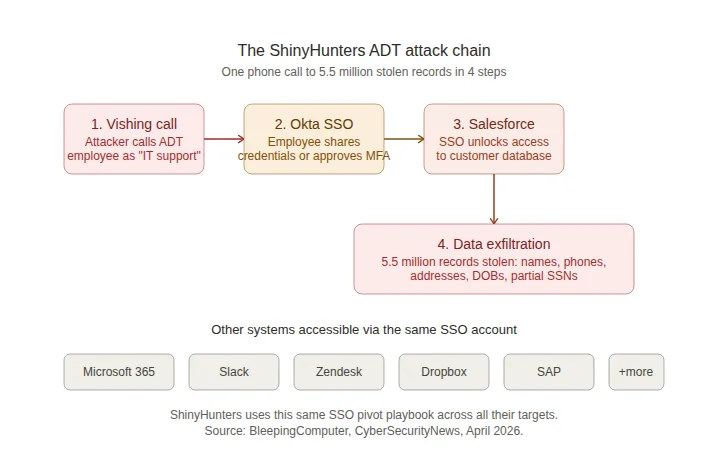
The largest home security company in America just got breached for the third time in a year. The attack didn't require a zero-day exploit, a malware payload, or a sophisticated technical intrusion. ShinyHunters called an ADT employee, convinced them to hand over access to their Okta single sign-on account, and walked into the company's Salesforce environment. 5.5 million customer records later, the group set a ransom deadline of today, April 27, 2026.
- ShinyHunters breached ADT on April 20, 2026, via a voice phishing (vishing) attack that compromised an employee's Okta SSO account
- Have I Been Pwned confirmed 5.5 million records exposed: names, emails, phone numbers, addresses, dates of birth, and partial Social Security numbers
- ShinyHunters used the compromised SSO access to pivot into ADT's Salesforce instance and exfiltrate customer data
- This is ADT's third disclosed breach in under 12 months (August 2024, October 2024, April 2026)
- No payment data or home security systems were compromised
- The ransom deadline is April 27, 2026 (today)
How a phone call broke into America's largest security company
The attack followed a playbook that ShinyHunters has refined across dozens of targets in 2025 and 2026. It starts with a phone call. Someone posing as IT support, a vendor, or a security team member contacts an employee and pressures them into sharing their login credentials or approving a multi-factor authentication prompt. The conversation is designed to create urgency: "We're seeing suspicious activity on your account. We need to verify your identity right now."
In ADT's case, the vishing attack compromised an employee's Okta single sign-on account. Okta SSO is a centralized authentication system that connects to dozens of internal applications with a single login. Once ShinyHunters had that one set of credentials, they didn't need to hack anything else. They logged into ADT's Salesforce instance (where customer data lives) using the same SSO access the employee used every day.
The attack exploited the exact problem that SentinelOne documented in their 2026 Annual Threat Report: when attackers operate with valid credentials, they look identical to a legitimate user. ADT's security systems saw an authorized login from an authorized account. The system can verify that the credentials are correct. It cannot verify that the person behind the credentials is who they claim to be.
A single compromised SSO account at a company the size of ADT can provide access to Salesforce, Microsoft 365, Google Workspace, Slack, Zendesk, Dropbox, and every other connected SaaS application. One phone call. Dozens of systems. Millions of records. This is why SentinelOne calls it the "Identity Paradox": more authentication tools than ever, and identity-based attacks are simultaneously harder to detect.
What was stolen
ADT confirmed that the stolen data includes names, phone numbers, and physical addresses. In a smaller percentage of cases, dates of birth and the last four digits of Social Security numbers or Tax IDs were also exposed. ADT stated that no payment information (bank accounts or credit cards) was accessed and that customer home security systems were not affected.
ShinyHunters claimed over 10 million records on their dark web leak site. ADT has not confirmed that number. Have I Been Pwned, the independent breach notification service, analyzed the stolen data and confirmed approximately 5.5 million unique records, including email addresses, names, dates of birth, phone numbers, physical addresses, and partial government-issued IDs.
That data might sound "basic" compared to a financial breach, but it's exactly what scammers need. Your name, address, and phone number are enough to craft a convincing phishing text ("Hi John, this is ADT security. We detected unusual activity at your home. Please verify your account at..."). Add the last four of your SSN and the attacker can attempt identity verification calls to your bank, your phone carrier, or your insurance company.
Third breach in a year
This is not ADT's first security incident. The company previously disclosed breaches in August 2024 and October 2024 that exposed customer and employee information. Three breaches in under 12 months from the largest home security company in the country raises a question that ADT customers deserve an answer to: what changed between breaches?
The fact that ShinyHunters was able to compromise an employee's SSO account through vishing suggests that either phishing-resistant MFA was not enforced on all SSO accounts, or that employee security awareness training did not adequately prepare staff for the specific social engineering tactics ShinyHunters uses. Both of these should have been addressed after the first two incidents.
For context, the Snowflake breach in 2024 followed a similar pattern: attackers exploited the fact that MFA wasn't mandatory, used stolen credentials, and breached AT&T, Ticketmaster, and Santander through a single vector. The lesson from Snowflake was clear: enforce MFA everywhere, no exceptions. ADT appears to have learned it the hard way, again.
Who are ShinyHunters?
ShinyHunters is one of the most prolific cybercriminal extortion groups operating today. Active since 2020, the group specializes in data theft followed by ransom demands. Their model is straightforward: breach, exfiltrate, extort. If the target doesn't pay, the data gets leaked or sold on their dark web site.
Their 2025-2026 target list reads like a Fortune 500 directory: the European Commission, Rockstar Games, McGraw Hill (13.5 million records), Carnival Corporation (Holland America Line, 7.5 million records), LVMH (Louis Vuitton, Dior, Tiffany), Google (corporate Salesforce instance), Qantas (5.7 million records), CarGurus (12 million records), and now ADT.
Multiple ShinyHunters members have been arrested and convicted. A French member, Sebastien Raoult, pleaded guilty in the US and faces up to 22 years in prison. A British member pleaded guilty in 2025. French authorities arrested four more members in June 2025. Despite the arrests, the group continues to operate and has expanded its campaigns in 2026.
Their refined playbook, which they've used successfully against ADT and dozens of other companies, follows a consistent pattern: vish an employee, compromise their SSO account (Okta, Microsoft Entra, or Google), pivot to connected SaaS applications (Salesforce, Microsoft 365, Slack, Zendesk), exfiltrate data, and extort the company with a public leak deadline.
What ADT customers should do right now
- Change your ADT account password. Use a password generator to create a unique, random password of at least 16 characters. Do not reuse a password from any other account.
- Change your email password too. If you used the same email and password combination for ADT and your email account, your email is now a target. Attackers will try the stolen credentials against common services. Your email account is the single most important credential you own because it controls password resets for everything else.
- Enable two-factor authentication. Turn on 2FA for your ADT account, your email, and your bank. Use an authenticator app (Google Authenticator, Authy, Microsoft Authenticator), not SMS. SMS codes can be intercepted through SIM-swapping attacks. For a deeper breakdown of 2FA options, check our 2FA vs MFA guide.
- Check Have I Been Pwned. Go to haveibeenpwned.com and enter your email address. The ADT breach has been added to the database. If your email appears, change the password on every account that uses that email address.
- Watch for phishing attempts. In the days and weeks following a breach, attackers use the stolen data to craft targeted phishing messages. Be suspicious of any text message, email, or phone call that references ADT, your home address, or your account. ADT will not call you and ask for your password or Social Security number. If someone does, hang up.
- Consider a credit freeze. If your date of birth and partial SSN were exposed, contact Equifax, Experian, and TransUnion to place a credit freeze. This prevents anyone from opening new accounts in your name. A freeze is free to place and remove.
One stolen credential gave ShinyHunters access to all of ADT's connected systems. Don't let the same thing happen to your accounts.
A password manager generates unique, random passwords for every account and stores them in an encrypted vault. If ADT's breach exposed a password you've reused elsewhere, a password manager is the fastest way to fix every account at once. NordPass includes breach monitoring that alerts you when your credentials appear in known leaks.
Try NordPass FreeAffiliate link. I may earn a commission at no extra cost to you.
The bigger pattern: vishing is the new phishing
The ADT breach fits into a broader trend documented across multiple 2026 threat reports. According to eSentire's 2026 Annual Cyber Threat Report, social engineering via email bombing and IT impersonation surged 1,450% year-over-year with a 72% intrusion success rate. ShinyHunters is one of the groups driving that number.
Traditional phishing (fake emails with malicious links) is something most security-aware people have learned to spot. Vishing is harder. A convincing voice on the phone creating urgency is a fundamentally different challenge than a suspicious email you can inspect at your own pace. The attacker controls the tempo of the conversation. They know your name, your role, your company. They sound like someone who belongs.
The defense against vishing at the personal level is simple: never share credentials or approve MFA prompts based on an incoming call. If someone calls claiming to be IT support or a vendor, hang up and call the organization back through a verified number. At the organizational level, the defense is phishing-resistant MFA (FIDO2 hardware keys or passkeys) that cannot be compromised through social engineering, because the authentication is cryptographically bound to the specific website and device.
For more on why credential theft is now the dominant attack vector and how passkeys eliminate the password attack surface entirely, see our analysis of the SentinelOne 2026 threat report.
Frequently asked questions
What happened in the ADT data breach 2026?
On April 20, 2026, the ShinyHunters extortion group breached ADT's systems by voice phishing (vishing) an employee and compromising their Okta single sign-on (SSO) account. Using that access, they infiltrated ADT's Salesforce instance and stole customer data including names, phone numbers, addresses, and in some cases dates of birth and partial Social Security numbers. Have I Been Pwned confirmed approximately 5.5 million records were exposed. No payment data or security system access was compromised.
How many people were affected by the ADT breach?
Have I Been Pwned analyzed the stolen data and confirmed approximately 5.5 million unique records were exposed, including email addresses, names, dates of birth, phone numbers, physical addresses, and partial government-issued IDs. ShinyHunters claimed over 10 million records, but ADT has not confirmed that number.
What is vishing and how did it breach ADT?
Vishing (voice phishing) is a social engineering attack conducted over the phone. The attacker calls an employee pretending to be IT support, a vendor, or a security team member, and convinces them to share credentials or approve a multi-factor authentication prompt. In ADT's case, ShinyHunters used vishing to compromise an employee's Okta SSO account, which gave them access to connected SaaS applications including Salesforce where customer data was stored.
What should I do if I'm an ADT customer?
Change your ADT account password immediately using a unique, randomly generated password of 16+ characters. Enable two-factor authentication on your ADT account and your email account. Check haveibeenpwned.com to see if your data appeared in this breach. Monitor for phishing attempts that reference ADT or your home address. Consider a credit freeze if your partial Social Security number was exposed. Be suspicious of any phone calls claiming to be from ADT's security team.
Who are ShinyHunters?
ShinyHunters is a cybercriminal extortion group active since 2020 that specializes in data theft and ransom demands. Their recent targets include ADT, the European Commission, Rockstar Games, McGraw Hill, Carnival Corporation, Google, Qantas, and many others. Multiple members have been arrested and convicted. The group has refined a repeatable playbook: vish an employee, compromise their SSO account, pivot to connected SaaS applications, exfiltrate data, and extort the company with a leak deadline.
Has ADT been breached before?
Yes. This is ADT's third disclosed data breach in under a year. The company previously reported breaches in August 2024 and October 2024 that exposed customer and employee information. The pattern of repeated breaches raises questions about whether ADT has adequately strengthened its identity and access controls between incidents.
Sources
- BleepingComputer: Home security giant ADT data breach affects 5.5 million people (April 27, 2026)
- BleepingComputer: ADT confirms data breach after ShinyHunters leak threat (April 24, 2026)
- Help Net Security: Hackers claim millions of records stolen in ADT breach (April 27, 2026)
- CyberSecurityNews: ADT Confirms Data Breach Following ShinyHunters Claim (April 25, 2026)
- The Record: ADT says customer data stolen in cyber intrusion (April 24, 2026)
- Wikipedia: ShinyHunters (updated April 2026)